[2017-New-Exams]Full Version SY0-501 Dumps 166Q for Free Download[101-110]
2017 November New CompTIA SY0-501 Exam Dumps with PDF and VCE Free Released Today! Following are some New SY0-501 Questions:
1.|2017 New SY0-501 Exam Dumps (PDF & VCE) 166Q&As Download:
https://www.braindump2go.com/sy0-501.html
2.|2017 New SY0-501 Exam Questions & Answers Download:
https://drive.google.com/drive/folders/1QYBwvoau8PlTQ3bugQuy0pES-zrLrRB1?usp=sharing
QUESTION 101
A security guard has informed the Chief Information Security Officer that a person with a tablet has been walking around the building. The guard also noticed strange white markings in different areas of the parking lot. The person is attempting which of the following types of attacks?
A. Jamming
B. War chalking
C. Packet sniffing
D. Near field communication
Answer: B
QUESTION 102
A system administrator is configuring a site-to-site VPN tunnel. Which of the following should be configured on the VPN concentrator during the IKE phase?
A. RIPEMD
B. ECDHE
C. Diffie-Hellman
D. HTTPS
Answer: C
QUESTION 103
A network operations manager has added a second row of server racks in the datacenter.
These racks face the opposite direction of the first row of racks.
Which of the following is the reason the manager installed the racks this way?
A. To lower energy consumption by sharing power outlets
B. To create environmental hot and cold isles
C. To eliminate the potential for electromagnetic interference
D. To maximize fire suppression capabilities
Answer: B
QUESTION 104
Phishing emails frequently take advantage of high-profile catastrophes reported in the news. Which of the following principles BEST describes the weakness being exploited?
A. Intimidation
B. Scarcity
C. Authority
D. Social proof
Answer: D
QUESTION 105
Users report the following message appears when browsing to the company’s secure site:
This website cannot be trusted. Which of the following actions should a security analyst take to resolve these messages? (Select TWO).
A. Verify the certificate has not expired on the server.
B. Ensure the certificate has a .pfx extension on the server.
C. Update the root certificate into the client computer certificate store.
D. Install the updated private key on the web server.
E. Have users clear their browsing history and relaunch the session.
Answer: BD
QUESTION 106
Drag and Drop Question
Drag the items on the left to show the different types of security for the shown devices. Not all fields need to be filled. Not all items need to be used.
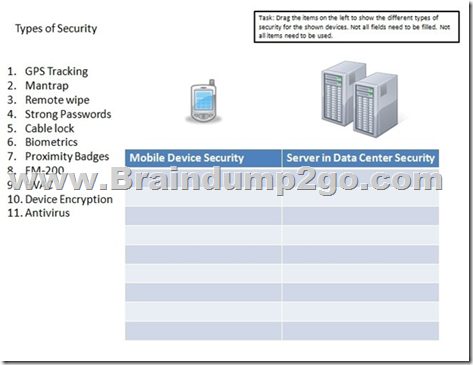
Answer:
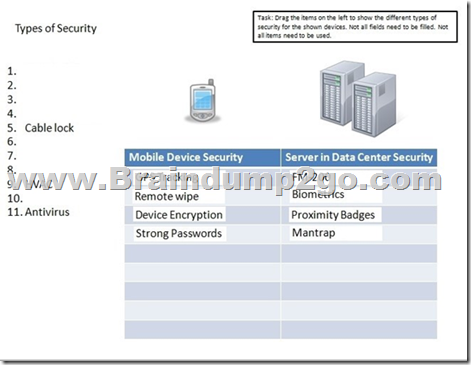
Explanation:
For mobile devices, at bare minimum you should have the following security measures in place:
Screen lock, Strong password, Device encryption, Remote wipe/Sanitation, voice encryption, GPS tracking, Application control, Storage segmentation, Asset tracking as well as Device Access control.
For servers in a data center your security should include: Fire extinguishers such as FM200 as part of fire suppression; Biometric, proximity badges, mantraps, HVAC, cable locks; these can all be physical security measures to control access to the server.
QUESTION 107
A company hires a consulting firm to crawl its Active Directory network with a non-domain account looking for unpatched systems. Actively taking control of systems is out of scope, as is the creation of new administrator accounts. For which of the following is the company hiring the consulting firm?
A. Vulnerability scanning
B. Penetration testing
C. Application fuzzing
D. User permission
Answer: A
QUESTION 108
Two users need to send each other emails over unsecured channels.
The system should support the principle of non-repudiation.
Winch of the following should be used to sign the users’ certificates?
A. CA
B. CRL
C. CSR
Answer: C
QUESTION 109
Multiple employees receive an email with a malicious attachment that begins to encrypt their hard drives and mapped shares on their devices when it is opened.
The network and security teams perform the following actions:
* Shut down all network shares.
* Run an email search identifying all employees who received the malicious message.
* Reimage all devices belonging to users who opened the attachment.
Next, the teams want to re-enable the network shares. Which of the following BEST describes this phase of the incident response process?
A. Eradication
B. Containment
C. Recovery
D. Lessons learned
Answer: A
QUESTION 110
Which of the following specifically describes the exploitation of an interactive process to access otherwise restricted areas of the OS?
A. Pivoting
B. Process affinity
C. Buffer overflow
Answer: A
!!!RECOMMEND!!!
1.|2017 New SY0-501 Exam Dumps (PDF & VCE) 166Q&As Download:
https://www.braindump2go.com/sy0-501.html
2.|2017 New SY0-501 Study Guide Video:
https://youtu.be/UBQZ5wOajbk